Why Heatmaps Are No Longer Enough: Translating Cyber Risk Into Financial Impact
For years, cybersecurity reporting has relied on a familiar visual: the red-yellow-green heatmap. It’s clean. It’s simple. It looks strategic.
And it is no longer sufficient.
As the CISO role has expanded from technical gatekeeper to enterprise risk architect, expectations have shifted dramatically. Boards are no longer asking, “How many critical vulnerabilities do we have?”
They are asking:
- What is our financial exposure?
- What is the probable loss if this scenario materializes?
- Are we investing proportionally to the risk?
- Are we defensible in the event of regulatory scrutiny?
Color gradients cannot answer those questions.
The Evolution of the CISO Mandate
A decade ago, the CISO’s responsibilities centered on controls, perimeter defense, and compliance checklists.
Today, the role spans enterprise risk management, regulatory interpretation, AI governance, executive communication, identity architecture, and measurable resilience outcomes
Cyber risk is now:
- A board-level governance issue
- A regulatory disclosure consideration
- A brand trust differentiator
- A potential legal liability
This shift demands a new reporting language — one grounded in financial impact, not operational severity.
Why Heatmaps Fall Short
Heatmaps communicate technical risk relative to other technical risks. They do not communicate business impact.
A vulnerability rated “High” does not tell a CFO:
- The potential revenue disruption
- The operational downtime cost
- The regulatory exposure
- The insurance implications
- The reputational impact
Worse, heatmaps often obscure prioritization. When everything is red, nothing is actionable.
Boards don’t want to see risk intensity. They want to understand risk exposure.
The Financial Risk Imperative
Leading organizations are shifting from qualitative scoring to scenario-based financial modeling. This does not require perfect precision. It requires defensible estimation.
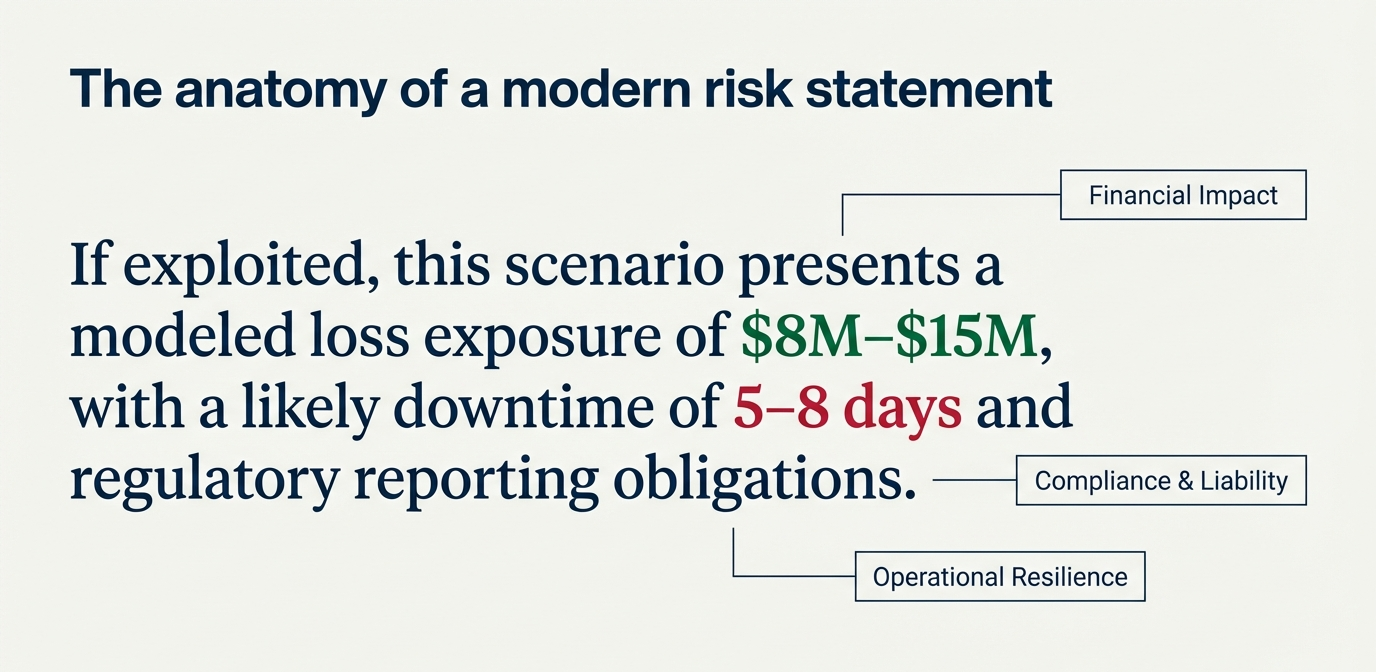
Instead of reporting:
“We have 17 critical vulnerabilities in internet-facing systems.”
Modern executive reporting sounds more like:
“If exploited, this scenario presents a modeled loss exposure of $8M–$15M, with a likely downtime of 5–8 days and regulatory reporting obligations.”
That changes the conversation.
Financial framing enables:
- Investment prioritization
- Executive alignment
- Regulatory defensibility
- Insurance optimization
- Clear board-level decision-making
It also strengthens the CISO’s executive credibility.
From Technical Metrics to Decision Metrics
This is not about abandoning operational dashboards. It is about elevating them.
Operational metrics answer:
- Are we detecting threats?
- Are we closing vulnerabilities?
- Are we meeting SLAs?
Executive metrics answer:
- What is our probable financial loss?
- Where are we under-invested relative to exposure?
- How does cyber risk compare to other enterprise risks?
- What is our residual risk after mitigation?
When CISOs connect detection performance to financial resilience, cybersecurity becomes an enterprise risk discipline — not just an IT function.
The CIO–CISO Alignment Moment
This shift also requires tighter alignment between CIO and CISO.
The CIO drives cloud adoption, AI deployment, product velocity, and infrastructure modernization. The CISO must quantify the risk introduced by those initiatives — in business terms.
Without financial translation:
- Security appears as a cost center.
- Innovation appears as a risk multiplier.
- Investment debates lack shared context.
Financial modeling creates a common language.
It moves the conversation from:
“Security is expensive.” to “This investment reduces modeled exposure by 37%.”
That is a board-ready statement.
Regulatory Pressure Is Accelerating the Shift
With evolving SEC disclosure expectations and increasing global regulatory scrutiny, organizations must demonstrate not only that they manage cyber risk — but that they understand its material impact.
Materiality is a financial concept.
This is why the modern CISO must operate as an enterprise risk translator, not simply a security operator.
What Comes Next
Heatmaps are not disappearing. But they are moving down the stack — from board presentation to operational management.
The next phase of cyber leadership requires:
- Scenario-based financial modeling
- Clear articulation of probable loss ranges
- Defined risk appetite thresholds
- Investment-to-risk-reduction mapping
- Executive-ready reporting frameworks
Organizations that fail to evolve will continue to struggle with budget alignment, regulatory defensibility, and board confidence.
Organizations that succeed will reposition cybersecurity as measurable enterprise resilience.
A Final Thought
Cybersecurity has crossed a threshold. It is no longer sufficient to show where risk exists. You must show what risk costs.
Because in 2026, the question isn’t: “How red is the map?”
It’s: “What is our exposure — and are we comfortable owning it?”
If your organization is still relying on qualitative risk scoring at the executive level, it may be time to assess whether your reporting model aligns with today’s board and regulatory expectations.